
As you might have noticed from the title, this is a bit of a weird one. In our last installment we managed to get our grade up to A from B finally, and while we’re not mounting our final assault for getting that A+ grade, I’d thought we’d mop up some of the more esoteric errors of the SSL Labs test. This isn’t a “score killer” so to say, and it doesn’t even seem to affect the final score. It’s also not very aptly named, since “ECDH public server param reuse” isn’t quite descriptive. I’ve tried researching what it exactly references to, but I’m drawing somewhat of a blank. As far as I’ve understood it, it pertains to the server reusing part of session keys when establishing new sessions, with the intent of saving some processing time by not having to regenerate these. However, I’ve not been able to find exactly why this is bad (even though generally speaking the term “reuse” shouldn’t be within a 10 foot radius of anything having to do with cryptography, just ask the WWII German Navy).

Nothing worse than a glaring warning
Anyhow, the folks over at SSL Labs are a lot smarter than I am, and it’s an easy fix on an F5 Big-IP, so we’ll fix it so we don’t have that error glaring at us on the test report. Also, it saves me from figuring out how to implement HSTS without breaking stuff for another week, so that’s a personal win for me as well.
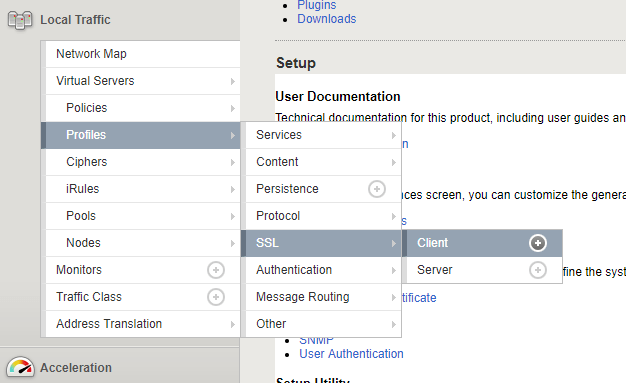
Again, we’re going to modify our SSL Client Profile, so head over to Local Traffic -> Profiles -> SSL -> Client and select the Profile you’d like to edit.
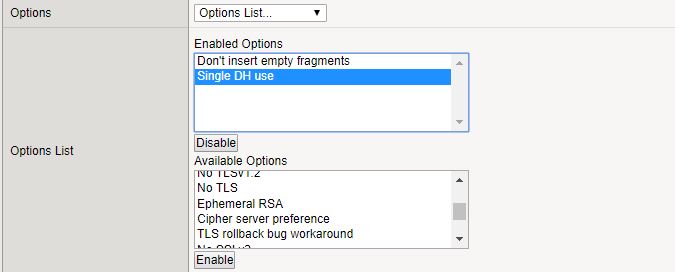
Enable the Advanced settings, and select the Options List as Custom for the profile

Find Single DH use under Available Options, select it and click Enable. It should jump up to the Enabled Options list.
That’s it, save your profile and that pesky error should be gone!
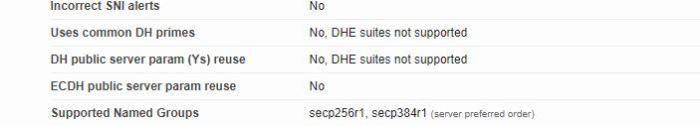
Huzzah, no error!
Also check out the other instalments of this series:
Fixing SSL Labs Grade on F5 Big-IP – Certificate Chains
Fixing SSL Labs Grade on F5 Big-IP – Weak Cipher Suites
Fixing SSL Labs Grade on F5 Big-IP – Disabling TLSv1 and TLSv1.1
Leave a comment