
Today we’ll take a look at fixing the error that kept us from getting a grade better than B last time.
Last time we were left with this test result:

“This server supports weak Diffie-Hellman (DH) key exchange parameters. Grade capped to B.”
This is a error pertaining to how the F5 suggests cipher suites to the client, and particularly, in what order. Sadly, this is a bit of a whack-a-mole, from time to time Qualys updates what they consider to be secure cipher suites, and then you need to go in and update your cipher lists. Usually, this happens once or twice a year. The problem is, that you can’t really just plainly disable all the older ciphers, as newer ones aren’t supported by older clients, so you need to disable the really old and horrible ciphers, while reordering them to always try the best ciphers first, and then falling back upon the less preferable ones until you find the best cipher that the client will support.
Luckily Mr. Kai Wilke of F5 has posted a short how-to on what cipher list to use, as well as an updated one when Qualys changed some things around.
So, according to Kai, the latest and greatest cipher list (as of Feb 2017) is the following, reproduced here for completeness sake:
!SSLv2:!EXPORT:!DHE+AES-GCM:!DHE+AES:!DHE+3DES:ECDHE+AES-GCM:ECDHE+AES:RSA+AES-GCM:RSA+AES:ECDHE+3DES:RSA+3DES:-MD5:-SSLv3:-RC4
So, now we need to apply this cipher list, and as luck will have it, it’s again under the SSL Profile that we improved last time.
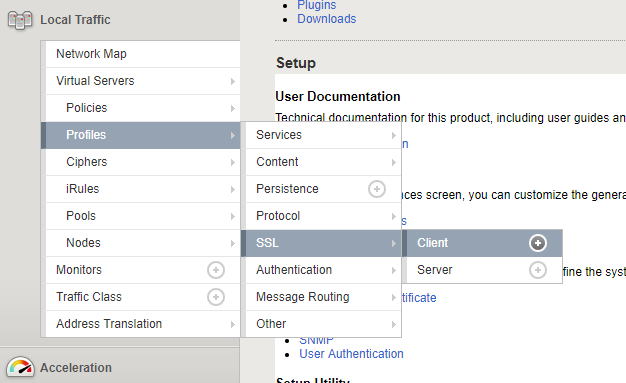
Go under Local Traffic -> Profiles -> SSL -> Client and select the Profile you’d like to edit.
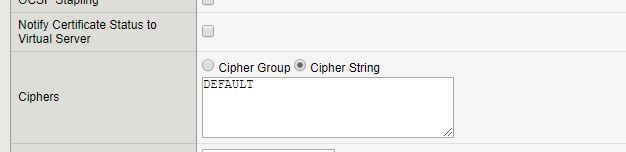
After selecting Configuration: Advanced at the top of the page, scroll down to Ciphers and check Custom at the right hand side.
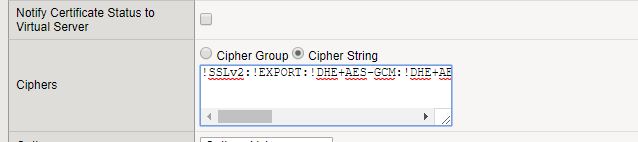
Click the radio button Cipher String and insert the string we borrowed from F5 into the text box.
After this you can just save your profile and rerun the SSL Test
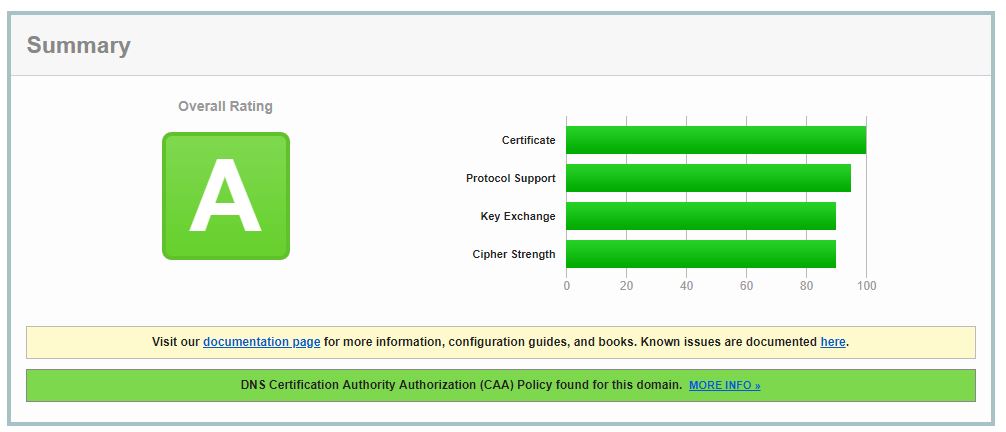
Which should give you the sought-after A Grade!
Also check out the other instalments of this series:
Fixing SSL Labs Grade on F5 Big-IP – Certificate Chains
Fixing SSL Labs Grade on F5 Big-IP – ECDH public server param reuse
Fixing SSL Labs Grade on F5 Big-IP – Disabling TLSv1 and TLSv1.1
Hey.
This is helpful as I’m in the midst of disabling the tls1.1.
May I know how you run the SSL Test?
It’s the test on ssllabs.com